Secure Logical Access for the Commercial Enterprise: Simple Solutions for an Urgent Need
Speak With An Expert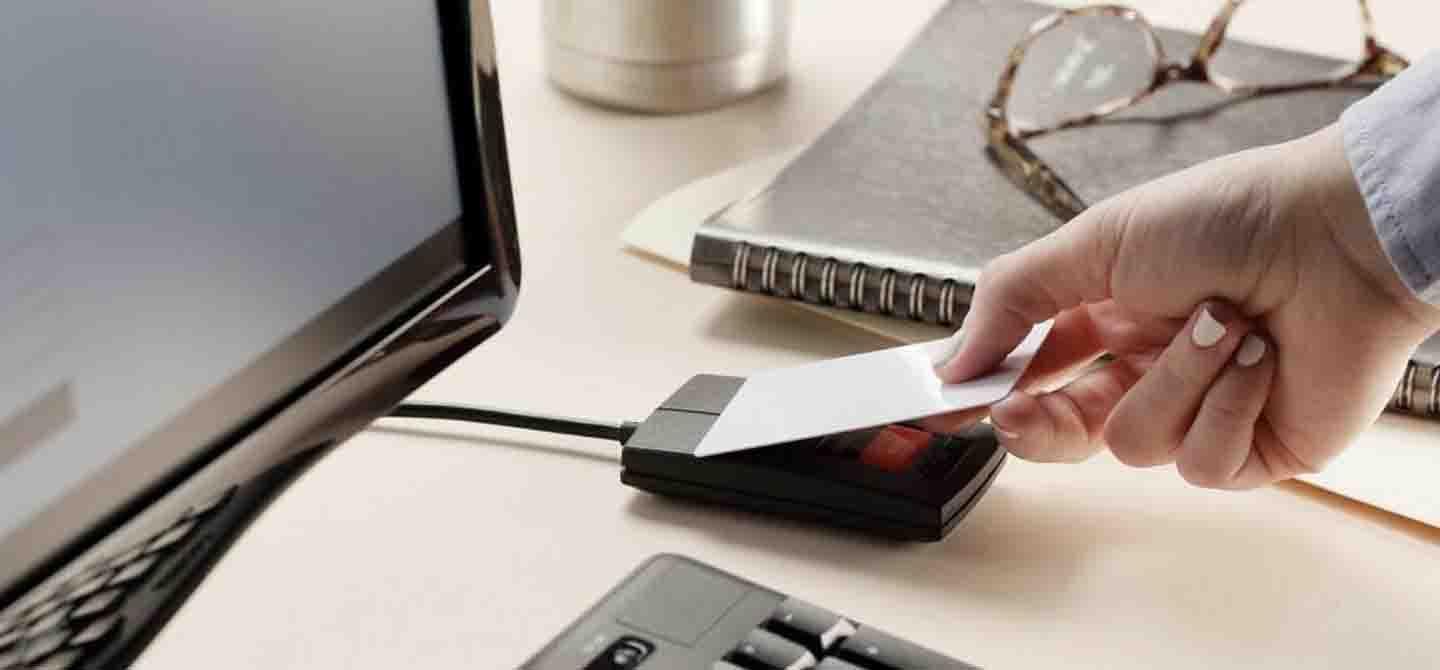
Hola mundo alerta alerta
Solutions
Discover the most durable, secure logical access control systems. rf IDEAS is backed by engineering and technical support to address any authentication need.
Transitioning away from legacy technology to modern credential solutions can enhance your organization's security. Explore various modern credential solutions including smart cards, mobile credentials, and FIDO passkeys to mitigate data breaches, unauthorized access, and phishing attacks.
Read moreSolutions
Main menu
Discover the most durable, secure logical access control systems. rf IDEAS is backed by engineering and technical support to address any authentication need.
Transitioning away from legacy technology to modern credential solutions can enhance your organization's security. Explore various modern credential solutions including smart cards, mobile credentials, and FIDO passkeys to mitigate data breaches, unauthorized access, and phishing attacks.
Read moreIndustries
Discover industry-specific digital access control systems, from healthcare to education, for your security-critical business needs.
Discover how RiverSouth Austin, in partnership with rf IDEAS, SwiftConnect, and Wavelynx, is transforming workplace access with digital company badges.
Explore videosIndustries
Main menu
Discover industry-specific digital access control systems, from healthcare to education, for your security-critical business needs.
Discover how RiverSouth Austin, in partnership with rf IDEAS, SwiftConnect, and Wavelynx, is transforming workplace access with digital company badges.
Explore videosProducts
WAVE ID® card readers are contactless access control solutions from rf IDEAS, the creators of pcProx card readers. Learn all about our RFID readers here.
Upgrade your existing physical and mobile credentials to the most secure authentication standard quickly and easily with the rf IDEAS ConvergeID™ Passwordless Platform. We’ll show you how.
Read moreProducts
Main menu
WAVE ID® card readers are contactless access control solutions from rf IDEAS, the creators of pcProx card readers. Learn all about our RFID readers here.
Upgrade your existing physical and mobile credentials to the most secure authentication standard quickly and easily with the rf IDEAS ConvergeID™ Passwordless Platform. We’ll show you how.
Read moreCredentials
Supporting the widest range of access control credentials and authentication credentials worldwide, rf IDEAS enables quick access and simplified authentication for organizations across the world.
Upgrade your access control with secure credentials. Explore smart cards, mobile credentials and FIDO2 passkeys for enhanced security and efficiency.
Read the BlogCredentials
Main menu
Supporting the widest range of access control credentials and authentication credentials worldwide, rf IDEAS enables quick access and simplified authentication for organizations across the world.
Upgrade your access control with secure credentials. Explore smart cards, mobile credentials and FIDO2 passkeys for enhanced security and efficiency.
Read the BlogPartners
As a member of the ENGAGE Partner Program, it’s simple to get the answers you need and the marketing materials and technical information that help build customer relationships.
Together, rf IDEAS and Imprivata Help Hospitals Authenticate Staff for Improved Care and Security
Read morePartners
Main menu
As a member of the ENGAGE Partner Program, it’s simple to get the answers you need and the marketing materials and technical information that help build customer relationships.
Together, rf IDEAS and Imprivata Help Hospitals Authenticate Staff for Improved Care and Security
Read moreSupport
Get all the support you need to be successful. Our support center provides product manuals, firmware and application downloads, software conversion tools, answers to frequently asked questions, and access to live technical and sales support
To assist our customers with the most common configuration needs, we have built out a library of self-serve Tech Tip videos to help you navigate how to use your rf IDEAS Configuration Utility.
Explore videosSupport
Main menu
Get all the support you need to be successful. Our support center provides product manuals, firmware and application downloads, software conversion tools, answers to frequently asked questions, and access to live technical and sales support
To assist our customers with the most common configuration needs, we have built out a library of self-serve Tech Tip videos to help you navigate how to use your rf IDEAS Configuration Utility.
Explore videosAbout us
rf IDEAS manufactures authentication solutions designed to simplify complex security problems and workflows across multiple industries.
Compare smart cards vs. mobile credentials, including key differences, benefits, risks and use cases to help determine the right authentication strategy.
Read the BlogAbout us
Main menu
rf IDEAS manufactures authentication solutions designed to simplify complex security problems and workflows across multiple industries.
Compare smart cards vs. mobile credentials, including key differences, benefits, risks and use cases to help determine the right authentication strategy.
Read the BlogSolutions
Discover the most durable, secure logical access control systems. rf IDEAS is backed by engineering and technical support to address any authentication need.
Transitioning away from legacy technology to modern credential solutions can enhance your organization's security. Explore various modern credential solutions including smart cards, mobile credentials, and FIDO passkeys to mitigate data breaches, unauthorized access, and phishing attacks.
Read moreSolutions
Main menu
Discover the most durable, secure logical access control systems. rf IDEAS is backed by engineering and technical support to address any authentication need.
Transitioning away from legacy technology to modern credential solutions can enhance your organization's security. Explore various modern credential solutions including smart cards, mobile credentials, and FIDO passkeys to mitigate data breaches, unauthorized access, and phishing attacks.
Read moreIndustries
Discover industry-specific digital access control systems, from healthcare to education, for your security-critical business needs.
Discover how RiverSouth Austin, in partnership with rf IDEAS, SwiftConnect, and Wavelynx, is transforming workplace access with digital company badges.
Explore videosIndustries
Main menu
Discover industry-specific digital access control systems, from healthcare to education, for your security-critical business needs.
Discover how RiverSouth Austin, in partnership with rf IDEAS, SwiftConnect, and Wavelynx, is transforming workplace access with digital company badges.
Explore videosProducts
WAVE ID® card readers are contactless access control solutions from rf IDEAS, the creators of pcProx card readers. Learn all about our RFID readers here.
Upgrade your existing physical and mobile credentials to the most secure authentication standard quickly and easily with the rf IDEAS ConvergeID™ Passwordless Platform. We’ll show you how.
Read moreProducts
Main menu
WAVE ID® card readers are contactless access control solutions from rf IDEAS, the creators of pcProx card readers. Learn all about our RFID readers here.
Upgrade your existing physical and mobile credentials to the most secure authentication standard quickly and easily with the rf IDEAS ConvergeID™ Passwordless Platform. We’ll show you how.
Read moreCredentials
Supporting the widest range of access control credentials and authentication credentials worldwide, rf IDEAS enables quick access and simplified authentication for organizations across the world.
Upgrade your access control with secure credentials. Explore smart cards, mobile credentials and FIDO2 passkeys for enhanced security and efficiency.
Read the BlogCredentials
Main menu
Supporting the widest range of access control credentials and authentication credentials worldwide, rf IDEAS enables quick access and simplified authentication for organizations across the world.
Upgrade your access control with secure credentials. Explore smart cards, mobile credentials and FIDO2 passkeys for enhanced security and efficiency.
Read the BlogPartners
As a member of the ENGAGE Partner Program, it’s simple to get the answers you need and the marketing materials and technical information that help build customer relationships.
Together, rf IDEAS and Imprivata Help Hospitals Authenticate Staff for Improved Care and Security
Read morePartners
Main menu
As a member of the ENGAGE Partner Program, it’s simple to get the answers you need and the marketing materials and technical information that help build customer relationships.
Together, rf IDEAS and Imprivata Help Hospitals Authenticate Staff for Improved Care and Security
Read moreSupport
Get all the support you need to be successful. Our support center provides product manuals, firmware and application downloads, software conversion tools, answers to frequently asked questions, and access to live technical and sales support
To assist our customers with the most common configuration needs, we have built out a library of self-serve Tech Tip videos to help you navigate how to use your rf IDEAS Configuration Utility.
Explore videosSupport
Main menu
Get all the support you need to be successful. Our support center provides product manuals, firmware and application downloads, software conversion tools, answers to frequently asked questions, and access to live technical and sales support
To assist our customers with the most common configuration needs, we have built out a library of self-serve Tech Tip videos to help you navigate how to use your rf IDEAS Configuration Utility.
Explore videosAbout us
rf IDEAS manufactures authentication solutions designed to simplify complex security problems and workflows across multiple industries.
Compare smart cards vs. mobile credentials, including key differences, benefits, risks and use cases to help determine the right authentication strategy.
Read the BlogAbout us
Main menu
rf IDEAS manufactures authentication solutions designed to simplify complex security problems and workflows across multiple industries.
Compare smart cards vs. mobile credentials, including key differences, benefits, risks and use cases to help determine the right authentication strategy.
Read the BlogMore than 1,000 data breaches have been reported in a single year In the United States at an average cost of $3.92 million each in losses and fines.1 Up to 88% of UK companies suffered data breaches in a single year at an average cost of £2.85 million. Successful hacks of small businesses in the UK occurred every 19 seconds.2
You could throw a dart at a map and find similarly horrifying statistics for any random country in the world. That’s the bad news.
Now, the good news
Many governments, vertical industries and even individual businesses recognize the scope of the problem and are responding. Identity and access management measures for healthcare and finance have long been commonplace and are now being adopted in commercial industries that have historically been security-lax.
Much of this is being driven by government laws and regulations, including:
These regulations call for a much more rigorous approach to data security than the single-factor password or PIN authentication methods that users have long been accustomed to.
Who do you trust?
In today’s connected world, you should trust no one until they can positively authenticate their identity. For example, President Biden’s Executive Order 14028 mandates that “all U.S. federal government agencies and all enterprises that serve them adopt a zero-trust architecture, where the answers to the questions of who, what, when, where, and how are critical for appropriately allowing or denying access to resources.” This includes adopting “[multi-factor] authentication and encryption of data both at rest and in transit.”
Considering all the companies that do business with the U.S. government, the reach of this order is very broad. Even businesses that aren’t directly affected by the U.S. presidential order see the writing on the wall and are moving quickly to implement two-factor authentication. In Europe, it’s already required under GDPR regulations—for example when accessing sensitive data such as patient medical records in a hospital, surgery or a walk-in vaccine center.
When data is compromised or leaked, the business is investigated to determine what steps were taken to protect data. If found to be neglectful, fines can run into millions of Euros. Increasingly, even individual citizens are waking up to the fear that their digital lives could easily be compromised to their personal, professional and financial detriment, in part due to high-profile news of celebrities who have had their personal information stolen and disseminated.
Multi-factor means authentic trust
Moving away from passwords and PINs to much more secure identifiers—such as the employee ID cards already used for building access—can vastly improve security in the commercial enterprise. And adopting multi-factor authentication (MFA) is key to achieving a true zero-trust architecture by requiring users to present more than one credential to access logical systems and networks.
Authentication factors can include “something you are” (such as a fingerprint), “something you have” (such as a physical ID card or digital mobile credential) and/or “something you know” (a password or PIN). Information systems are 99.9% less likely to be compromised when users present two or more of these factors instead of just one.3
However, MFA represents a big change, bringing challenges and concerns for hardware manufacturers and independent software vendors, their commercial business customers, and end users alike.
For hardware vendors, how can they ensure that authentication hardware can communicate with host systems from all fixed and mobile devices? How can they offer a simple, quick authentication experience that seamlessly connects to the solutions their commercial customers have implemented for single sign-on?
For ISVs, how can they provide for fast, error-free login while helping their commercial customers enforce a zero-trust policy across the enterprise? How can they enable multi-factor authentication while supporting the employee credentials their customers have already invested in?
For end users, how can they log in quickly and seamlessly, so they can focus on work? How can they log in wherever and whenever they need to, even remotely or from a home office, without feeling as if they’re being monitored—but rather with confidence that their identity, location and data are being shielded from discovery by bad actors?
For commercial enterprises, how can they implement a multi-factor authentication approach in support of a zero-trust policy without excessive costs, delays or disruptions to the business? How can they sustain the productivity and satisfaction of their employees?
Dynamic multi-factor authentication is the answer
Commercial enterprises typically have a large number of different logical access points, used in different ways by different user groups. Dynamic MFA supports the requirements of each user by enabling a choice of multiple authentication factors at each access point.
For example, dynamic MFA could mean supporting existing proximity and smart card credentials while adding an authentication factor such as a biometric fingerprint. It could mean providing smartphone-based digital credentials that allow employees to work across work sites or even across national borders without the need to carry multiple physical badges. It could mean supporting different credentials and combinations for different use cases.
For example, a user might access the office garage without ever opening the car window or even stopping, using a digital credential that is detected via the user’s Bluetooth® Low Energy-enabled smartphone. The same user might then access a workstation or release a secure print job by waving a physical ID card or their smartphone-based digital credential, which is programmed with the same ID number as their physical badge.
rf IDEAS makes MFA simple
Implementing these dynamic MFA scenarios for different users and different access points may sound hopelessly complicated—even more so if the enterprise is large and geographically distributed.
But together with our ISV partners, rf IDEAS offers physical and mobile credential readers in a wide variety of form factors, with solutions that can easily be added to or integrated within tablets, notebooks, desktops, secure printers and other devices to add a second authentication factor on top of existing password or PIN-based security protocols.
And rf IDEAS has a simple solution that preserves existing security infrastructure—such as employee ID cards—while supporting multiple authentication factors, in multiple combinations, within a single device:
WAVE ID® Bio: multi-factor authentication in a single reader
Our WAVE ID Bio reader combines a proximity and smart card reader, a Bluetooth Low Energy reader, and a biometric fingerprint reader in a single plug-and-play device that consumes only one USB port. It’s sleek and modern; it’s easily adaptable to practically any access point and MFA scenario; it’s plug and play with Windows 10; and it’s a pleasure to use.
For hardware vendors, WAVE ID Bio offers the simplest solution for integrating MFA through a single, compact reader. USB connectivity provides universal compatibility with modern systems, both fixed and mobile authentication. We also offer a complete range of low-frequency, dual-frequency and digital credential readers readers, including tiny, ruggedized options for mobile use and embedded options for direct integration within OEM devices. And our extensive partner network delivers a wealth of options for integrating WAVE ID® readers with existing networks and single sign-on solutions.
For ISVs, WAVE ID readers support a wide variety of authentication protocols, including CCID, keyboard emulation and raw data. Support for FIDO2 technology enables passwordless authentication that works seamlessly across devices and platforms. And our universal SDK enables developers to easily provide a single application that supports nearly any credential in use worldwide.
For end users, rf IDEAS readers offer the simplest, quickest way to securely authenticate to the systems they need—wherever they need—so they can get right to work. With WAVE ID Bio, multi-factor authentication is as simple as presenting a physical and/or digital credential and/or touching a fingerprint sensor—all in a couple of seconds and on a single reader. Plus, users can rest assured that their credential and biometric information is encrypted and secured by the authentication software—never stored on the reader itself.
For commercial enterprises, identity and access management technologies from rf IDEAS and our partners provide the simplest, most direct path to the zero-trust data security required by government regulations and today’s business realities.
Want to learn more?
rf IDEAS has the ideas and technology you need to secure your enterprise data with confidence, contact your rf IDEAS representative today.
1. Cost of a data breach report 2020, IBM.
2. UK cybersecurity statistics you need to know, CSO Online.
3. www.techbeacon.com/security/state-mfa-4-trendsportend-end-solo-password
Please note: The information you provide in this form will help us direct you to the appropriate partner who can best fulfill your request.