47% of identity and access managers say mobile authentication boosts security
Mobile.
Access More.
By 2024, there will be more than 120 million downloads of mobile credentials. End the risk of passwords and the time and expense of managing physical ID badges. Mobile credentials offer instant, secure authentication using the one tool everyone already carries: a smartphone.

WAVE ID Plus Mini
Small size meets superior security. 35% smaller than the original, the WAVE ID Plus Mini offers the same versatility but in a smaller package. Its sleek, modern design minimizes clutter and increases space while easily integrating into your existing system.
See Product
WAVE ID Bio
WAVE ID Bio incorporates the rf IDEAS flagship WAVE ID platform, capable of reading most global proximity and contactless credentials, with Bluetooth® Low Energy technology and a fingerprint sensor from Crossmatch.
See Product
WAVE ID SP Plus
Versatile and scalable, the WAVE ID SP Plus combines proximity and contactless technologies into one reader, while the WAVE ID SP offers convenience for users who only utilize contactless credentials.
See Product
WAVE ID Nano
It is the world’s smallest badge reader. The WAVE ID Nano reader delivers all the features of desktop and surface-mount readers in an ultra-compact format. It is available for use with the traditional USB-A port or in an even smaller USB-C version to fit newer laptops, tablets and smartphones.
See Product
WAVE ID Mobile
Today’s smartphones offer artificial intelligence capabilities that support a robust digital persona. To better support an increasingly mobile workforce, rf IDEAS® offers dual-frequency readers that incorporate a Bluetooth® reader for access control using industry-leading mobile credentials in addition to reading 125 kHz proximity or 13.56 MHz contactless smart cards.
See ProductMore versatility, more security
Streamline workflow and identification errors by eliminating manual entry of user names and passwords with built-in multi-factor authentication.
A look at the smallest reader yet
It’s tiny, but tough and built for any authentication challenge, even in the most demanding environments.
Where mobility meets access
Is mobile access right for you? Wherever traditional credentials are used, mobility delivers a trusted contactless tool in a safe form factor that everyone already uses.
Access for any needs
From hospitals to banks to manufacturing, provide security across the organization while eliminating the risks and frustrations of misidentification.
Identity + Access Management
Are your users burdened with repeatedly typing and mistyping passwords throughout the workday? Do frequent password resets cost unnecessary time and money? Have you truly secured every access point to your network?
Source: 2022 ForgeRock Consumer Identity Breach Report
Learn More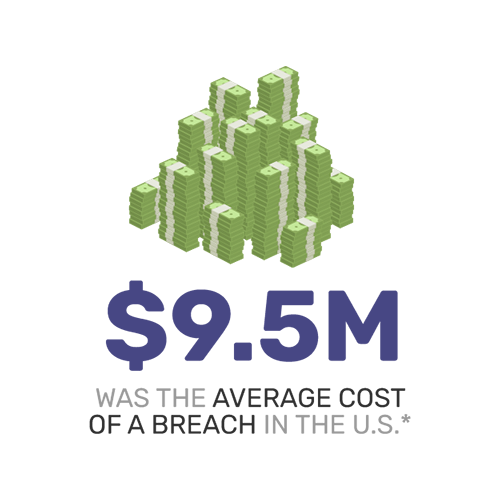
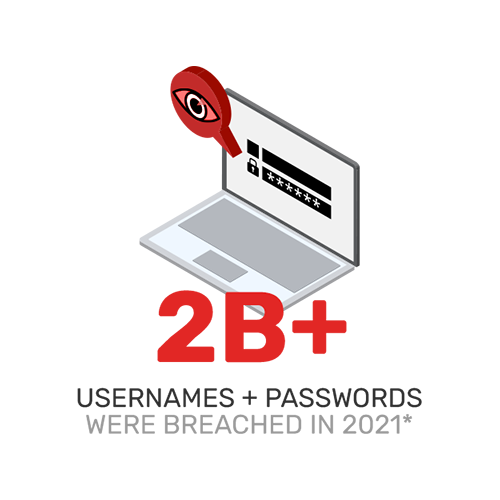
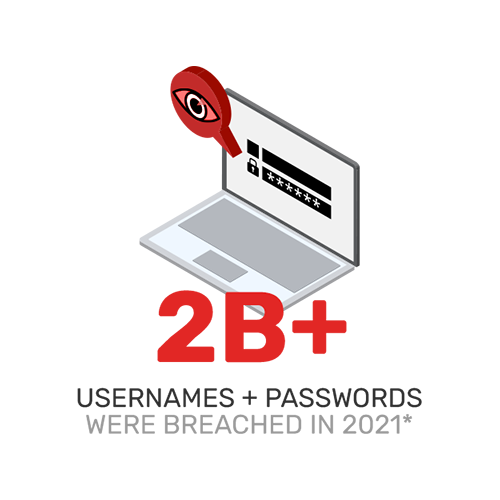
Multi-Factor Authentication
What would a data breach cost? Do you need to comply with privacy and zero-trust mandates? How can you achieve the trust of multi-factor authentication without interrupting workflows or impairing productivity?
Source: 2022 ForgeRock Consumer Identity Breach Report
Learn More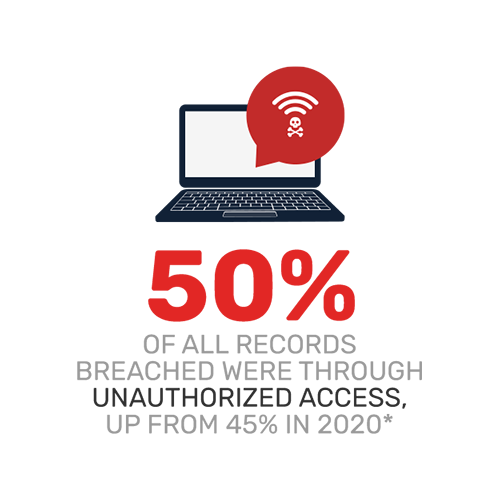
Secure Print Management
Are your printers vulnerable to stolen documents, whether physical or digital? Could they provide the network access an attacker is looking for? What are your total costs for printing personal files or documents that no one ever picks up?
Source: 2022 ForgeRock Consumer Identity Breach Report
Learn More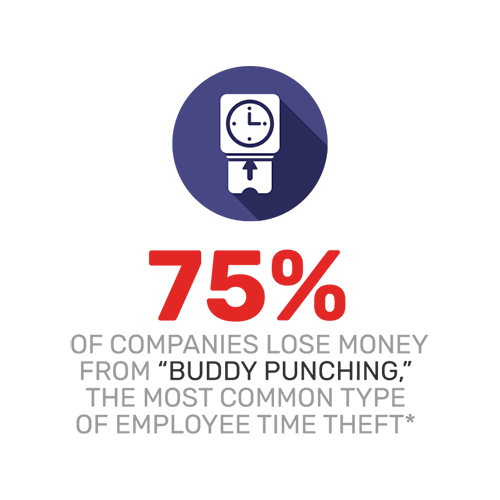
Time and Attendance
Do you have trouble accounting for individual attendance at work, in required meetings or in classrooms? Have you ever encountered abuse of a paper-based time and attendance solution, or had difficulty demonstrating compliance?
Source: American Payroll Association
Learn More
Mobile Authentication
Is your staff always on the go, authenticating to different workstations, in different rooms and offices, at hotels or other remote locations? Do you need help choosing the right mobile solution and integrating into your current system?
Source: IBM Cost of a Data Breach Report 2022
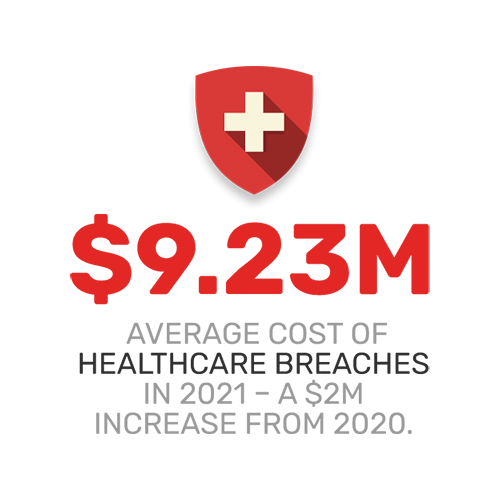
Biometric Authentication
Are you looking for the simplest way to comply with HIPAA, EPCS, the Zero Trust executive order or other mandates? What if you could achieve multi-factor authentication in a single device, with no usernames or passwords required?
Source: IBM Cost of a Data Breach Report 2021
Identity + Access Management
Are your users burdened with repeatedly typing and mistyping passwords throughout the workday? Do frequent password resets cost unnecessary time and money? Have you truly secured every access point to your network?
Source: 2022 ForgeRock Consumer Identity Breach Report
Learn More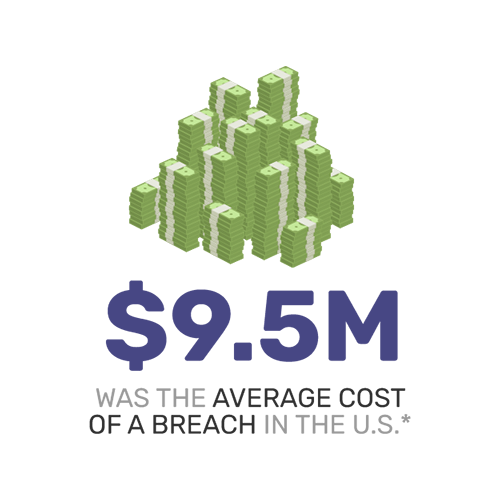
Multi-Factor Authentication
What would a data breach cost? Do you need to comply with privacy and zero-trust mandates? How can you achieve the trust of multi-factor authentication without interrupting workflows or impairing productivity?
Source: 2022 ForgeRock Consumer Identity Breach Report
Learn More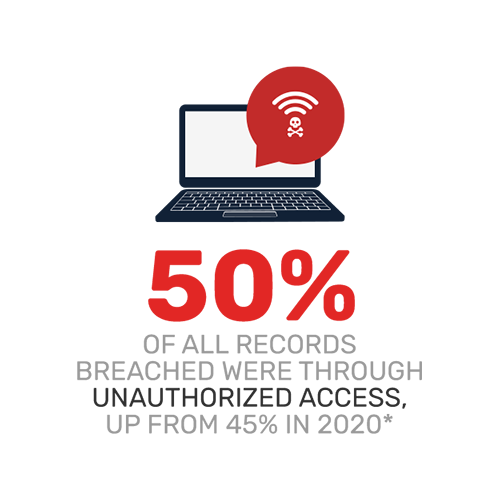
Secure Print Management
Are your printers vulnerable to stolen documents, whether physical or digital? Could they provide the network access an attacker is looking for? What are your total costs for printing personal files or documents that no one ever picks up?
Source: 2022 ForgeRock Consumer Identity Breach Report
Learn More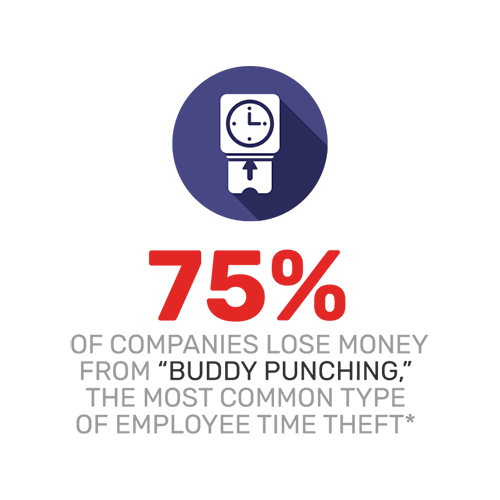
Time and Attendance
Do you have trouble accounting for individual attendance at work, in required meetings or in classrooms? Have you ever encountered abuse of a paper-based time and attendance solution, or had difficulty demonstrating compliance?
Source: American Payroll Association
Learn More
Mobile Authentication
Is your staff always on the go, authenticating to different workstations, in different rooms and offices, at hotels or other remote locations? Do you need help choosing the right mobile solution and integrating into your current system?
Source: IBM Cost of a Data Breach Report 2022
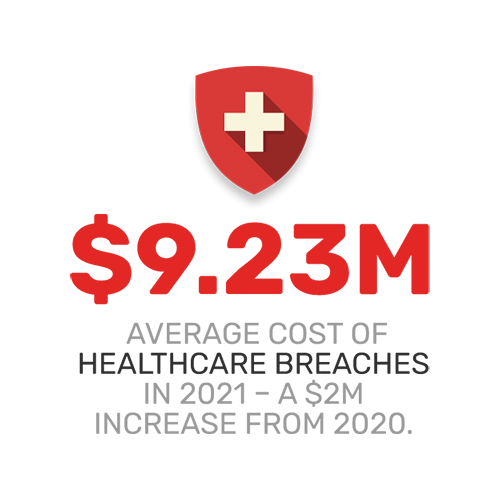
Biometric Authentication
Are you looking for the simplest way to comply with HIPAA, EPCS, the Zero Trust executive order or other mandates? What if you could achieve multi-factor authentication in a single device, with no usernames or passwords required?
Source: IBM Cost of a Data Breach Report 2021
More than 80% of data breaches are caused by stolen, weak or default passwords, and almost 70% go undetected for up to several months.
For 25 years and counting, rf IDEAS has been taking authentication solutions beyond the front door to where work gets done.
The global contactless smart card market is expected to grow at a compound annual growth rate of 18% through 2027.
There are hundreds of proximity and contactless smart card brands and types in use worldwide. WAVE ID card readers are compatible with nearly every one.

Improving security and safety of hospital workflows

Why Implement MFA?

What’s Happening

What Is Passwordless Authentication & How Does It Work?
How does passwordless authentication work? Learn how it replaces passwords with secure alternatives and where it delivers the most value across industries.

rf IDEAS Named One of the 2025 North America Inspiring Workplaces
We’re proud to share that rf IDEAS has been ranked #93 on the 2025 North America Inspiring Workplaces list! This recognition celebrates the people and culture that make our company truly exceptional.
The Password Trap: What Its Costing Your Business (And How to Escape)
Raul Cepeda Jr., VP of Product & Marketing at rf IDEAS, joins the UnHacked podcast to expose the real costs of password fatigue—and how businesses can move toward secure, passwordless authentication.